Black Hats and White Hats
Santosh Nongthombam *
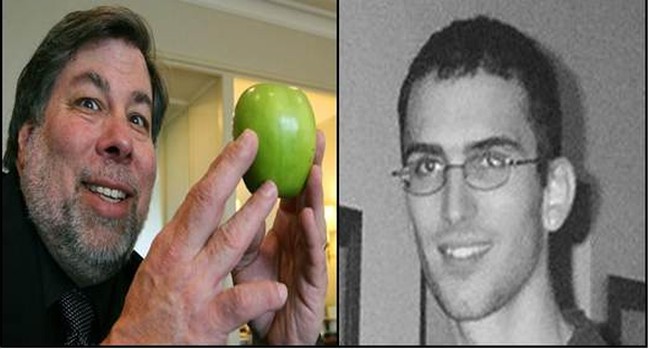
( Left-Right): Steve Wozniak , Jonathan james
Who are these Black Hats and the White Hats and what is he going to talk about? Perhaps this is the first question that would strike upon reading the title. I am not referring to different races or people, not even different kinds of hat. Some people might already havean idea about what I am going to talk about. However, the majority would not know that these are the categorization that the Hacking world is broadly split into. Yes, we will walk along the shores of the world of Hacking.
For any young techie or a student learning the ways of the computer and networking. Hacking has always been a subject of intrigue and admiration. Almost every young technology driven soul admired and wanted to be like them. These guys are the cream of the IT lot, the geniuses, the best of all the developers in the world, the king of coders. Also, over the years Hollywood movies have played their part in creating this Godly image of the hackers. If you remember the young guy in Die Hard 4.0, The Matrix or even the more recent-The social Network.
Word Hacker was coined in the 60's in AI Labs of MIT (Massachusetts Institute of Technology) to describe individuals with exceptional computing skills and someone who pushes the boundaries of programmable system. However, it is now more used in the context of someone using his / her extraordinaire computing skills with malicious intent. The Cyber Ninja as we call them. Few of the common tools that are currently used by hackers throughout the world are Open source- Network exploration, password cracker, OS fingerprinting tool, network/packet sniffer and few more. We will get into further details of what each tool does and their capability in further articles. For now, I would like to share the surface story and few people who have greatly influenced the world of hacking.
To begin with, Lets understand who these Black Hats and White Hats are:
Black Hats: These are the bad guys. The nerds who are out there to rule the Cyber World with a chip on their shoulder. Give them a system and access to internet and they break into your source code, create virus, cause disruption, and bring down servers. They are what Hollywood often brings to our TV screen.
White Hats: These are the good guys. They are the security expert who loves to play around with source codes and network securities with no intention of causing harm to the system. We often see them as network security consultants, advisors, Web guru etc. You might be surprised that some of the big names in IT corporate world fall in this category. And they too by default are Hackers!
Let's talk about some of the more popular Black Hats.
Jonathan James (1983-2008): Jonathan James a.k.a. "c0mrade" is one of the most popular names in the CyberWorld. He is the first juvenile, 16 year old who was sent to prison for cybercrime. He first came into limelight for installing Backdoor in United States department of defense servers. Backdoor is used to bypass normal authentication, secure remote access to a computer/server and remain undetected all the while.
He also went ahead and hacked into NASA's network and downloaded source code for International Space Station. This whole episode cost NASA $41,000 to check and fix its system. Year 2007 saw a wave of malicious network attacks. James, who denied any involvement with it was suspected and interrogated. In 2008, James committed suicide leaving a note that read. ""I honestly, honestly had nothing to do with TJX. I have no faith in the 'justice' system. Perhaps my actions today, and this letter, will send a stronger message to the public. Either way, I have lost control over this situation, and this is my only way to regain control. I die free." A sad end to an amazing computing talent.
Adrian Lamo (Born 1981): Adrian first came into limelight for breaking into several high profile computer networks including New York Times and Microsoft. He is popularly referred to as the 'Homeless Hacker'. He also performed attacks on Yahoo, Citigroup, BOA and Cingular. He was fine $65,000 and 6 months of house arrest.
Kevin Mitnick (Born 1963): Born in 1963, Kevin was the most wanted cybercrime criminal at the time of his arrest. Also known as 'Condor' he was arrested in 1995 for multiple cybercrime. He bypassed the LA bus pass system and also indulged in phone hacking. He was convicted for breaking into Digital equipment, corporation's network and stealing software. He spent 5 years in prison with 8 months in solitary. Kevin now works as a computer security consultant, author and speaker.
Kevin Poulsen(Born 1965): Kevin is a former Black Hat hacker and now works as the senior editor of Wired News. He once hacked into a radio station's phone line and fixed himself as the eventual winner of a contest which won him a Porsche. He is also known as the 'Dark Dante'. He then broke into FBI's federal system and stole wiretap information. He served 5 years prison upon conviction.
Other than the above Black Hats, Few white Hats that equally deserve a mention are:
Stephen Wozniak (Born 1950): We have all heard of Steve Jobs. Well Steve Woxniak is the 'Other Steve of Apple' and the Technical Brain behind it. Before Apple, Steve made a device that could bypass traditional telephone switch mechanism and make long distance calls for free.
Tim Berners Lee (Born 1955): Tim is the founder of world wide web. The system that we all use to navigate the internet to access different files, folders etc. To his credit, Tim when he was a student in Oxford University built a computer from scratch using a soldering iron, TTL gates, an M6800 processor, and parts from an old television.
Linus Torvalds (Born 1969): Linus Torvalds as we know is the Father of Linux. He created the first Linux kernel in 1991 using the Minix operating system. Linux has grown in popularity over the last two decades and is the only possible substitute for the obvious MAC and Windows.
Few other white Hats who have had significant impact to the computing world are Richard Stallman, Jullian Assange and Mark Zukerberg of Facebook. Many more names I might have missed, do share if you know of any.
Black Hats or White Hats, whichever category these people belong to. They have all contributed enormously to cyber security and computing world as a whole. They found flaws in flawless systems. They are the Zeus and Hades of the Cyber World and are intertwined in a never ending struggle for Cyber supremacy. The above one's came out in open. Perhaps the greatest ones were never caught and are still at large. We never know when they will strike again.
* Santosh Nongthombam (from Bangalore) wrote this article for e-pao.net
The writer can be contacted at santos(dot)myself(at)gmail(dot)com
This article was posted on October 03, 2012.
* Comments posted by users in this discussion thread and other parts of this site are opinions of the individuals posting them (whose user ID is displayed alongside) and not the views of e-pao.net. We strongly recommend that users exercise responsibility, sensitivity and caution over language while writing your opinions which will be seen and read by other users. Please read a complete Guideline on using comments on this website.